Category: ERP Reporting
InOrder Packing Verification Provides Heads Down, Hands Free Data Entry
With the InOrder Packing Verification Enhancement, your warehouse personnel can scan and pack items to record and verify the contents of individual shipments. As items are scanned, InOrder compares what was packed with what was ordered and allocated.
InOrder reports to the packer with distinct audible signals throughout the process. This speeds the verification process by not requiring the packer to constantly view the results on the screen. When the order is complete, the shipment is accepted.
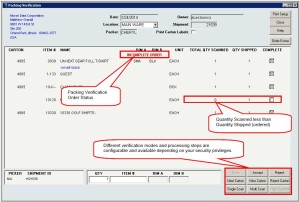 Packing is at the shipment level and recording is at the order level. InOrder can check for unprinted / ready to print orders that are shipping to the same customer as the shipment currently being packed.
Packing is at the shipment level and recording is at the order level. InOrder can check for unprinted / ready to print orders that are shipping to the same customer as the shipment currently being packed.
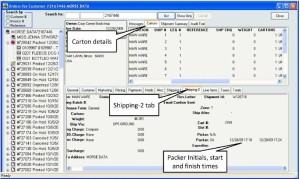
Picker and packer initials are recorded, along with carton details and shipment summary.
 The InOrder Packing Verification provides three different packing verification methods:
The InOrder Packing Verification provides three different packing verification methods:
- Single Scan – Each unit in the shipment is individually scanned. This method is used when line item quantities are typically low enough to scan each unit.
- Multi Scan – This method is used when line items often have higher quantities, so the process is streamlined for keying in the quantity when a line item has more than one unit to ship.
- High Quantity – This method allows quicker packing verification when the quantities are unusually large and difficult to count during packing. Each SKU is scanned once, regardless of quantity to be packed in a single carton.
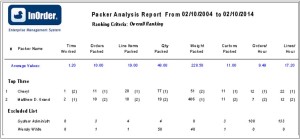
The Packer Analysis Report provides at-a-glance analysis of packer productivity.
 When you pack your shipments with InOrder, you can assemble all available items for the shipment at the packing station, use picking forms or produce separate packing slips, pack cartons for EDI orders, and track lot or serial numbers. You can even control if a shipment can be posted without packing verification.
When you pack your shipments with InOrder, you can assemble all available items for the shipment at the packing station, use picking forms or produce separate packing slips, pack cartons for EDI orders, and track lot or serial numbers. You can even control if a shipment can be posted without packing verification.
For more information about the InOrder Packing Verification Enhancement, contact sales@morsedata.com.
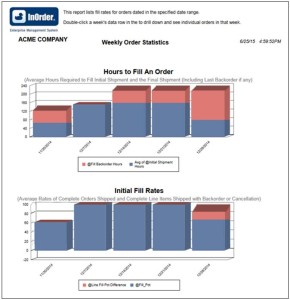
Use Order Fill Rate to Measure Customer Service
The F. Curtis Barry & Company, a consulting company that provides solutions for multichannel operations and fulfillment, recommends that multichannel companies use Initial Order Fill Rate (IOFR) to measure customer service and inventory availability by order.
We agree. Both of these metrics are provided on InOrder’s Order Statistics Report. This data shows where you stand in regards to providing what customers expect – that inventory is available when ordered, and orders are shipped in a timely manner.
Initial fill rates are shown for orders within a range of weeks that you specify, along with the average number of hours it takes to fill those orders.
 For the complete article by F. Curtis Barry & Company, click here.
For the complete article by F. Curtis Barry & Company, click here.
New InOrder ERP Reports to Encourage Customers to Place Orders
Loyalty Programs give customers incentives to buy. They provide benefits for both your business and your customers by generating income and expressing appreciation to your customers. Companies from grocery stores to your local day spa use loyalty award programs to help keep customers coming back, increase sales, and improve customer engagement.
Two new reports, Loyalty Point Expiration Card and Loyalty Account Statements, have been added to the InOrder ERP Loyalty Program Enhancement.
The Loyalty Point Expiration Card is used to generate postcards to send to customers when their loyalty points are nearing expiration.
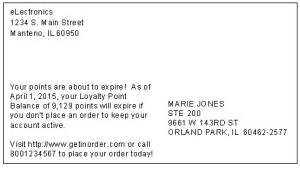 Loyalty Account Statements are generated with the customer’s loyalty point activity and balance.
Loyalty Account Statements are generated with the customer’s loyalty point activity and balance.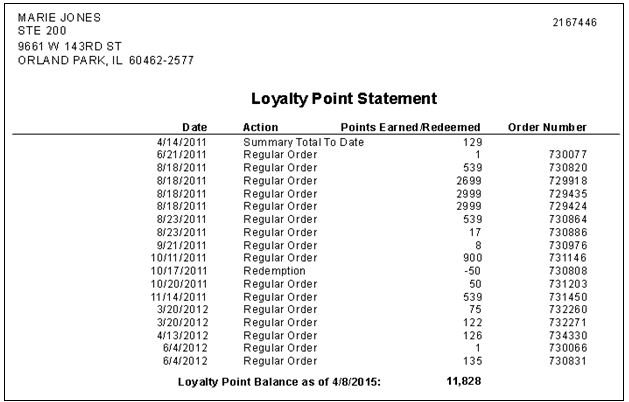
Contact us for more information about the InOrder Loyalty Program Enhancement.
Protecting Against Theft with ERP Software
Employee theft goes well beyond loss of cash or product to get to your bottom line. It can affect your customers by way of higher prices and inferior shopping experiences, which can have a direct impact on your reputation. Imagine what your customer thinks of your business when he or she is promised an item by a specific date because you think you have it in stock. Although your (paper) records showed you had the item, it was ultimately backordered. Unfortunately, the item was stolen by an employee and you were not aware until the customer was already disappointed.
And speaking of your reputation, you don’t want to invite even more shoplifting because your business is known as an easy target.
Employee theft can also affect other employees. Stealing from you indirectly steals from them. How many times will it happen before other employees question whether you’re competent enough to keep the business strong and safe? After it happens, will you unfairly limit the freedoms of the rest of your staff?
Software Advice™, a consultancy that analyzes inventory management software, recently released the results of a study exploring how inventory management software can detect employee theft.
The survey questioned U.S. retail employees about store types, job titles, inventory management methods, theft perception, and outright stealing from their employers.
According to the report, the National Retail Federation (NRF) estimates that employee theft accounted for almost 44% of total losses for US retailers. Some of the data revealed from responses to the survey from Software Advice™ included the following:
- 85% of national retail chains, 53% of local and regional retail chains, and 37% of small stores surveyed use inventory management software.
- Only 28% of employees whose stores use inventory management software said internal theft is a problem, compared to 37% of employees whose stores use other methods for managing inventory.
- 22% of employees at stores without inventory management software openly admitted to stealing products, compared to 15% of employees whose stores use inventory management software.
As explained in the report, modern inventory management systems can be integrated with other software and hardware to detect suspicious patterns, providing data for management involvement.
 For example, when you use a quality ERP system, your inventory availability is tied directly to your order system. The InOrder ERP system includes audit logging, which provides dates, user names, and tasks each user performs. The inventory on hand is tracked for the duration of its time in the warehouse. Any inventory transactions including receipts, sales, returns, as well as all types of adjustments, such as kit assemblies, facility transfers, inter-facility bin moves and replenishments, cycle count adjustments, damaged write-offs, etc. are tracked to allow precise SKU audits. Additionally, full warehouse “snapshots” of quantity and value on hand are taken whenever an accounting period is closed, allowing reports to show beginning on hand, activity, and ending on hand for an accounting period. Inventory accuracy typically approaches 99.9%.
For example, when you use a quality ERP system, your inventory availability is tied directly to your order system. The InOrder ERP system includes audit logging, which provides dates, user names, and tasks each user performs. The inventory on hand is tracked for the duration of its time in the warehouse. Any inventory transactions including receipts, sales, returns, as well as all types of adjustments, such as kit assemblies, facility transfers, inter-facility bin moves and replenishments, cycle count adjustments, damaged write-offs, etc. are tracked to allow precise SKU audits. Additionally, full warehouse “snapshots” of quantity and value on hand are taken whenever an accounting period is closed, allowing reports to show beginning on hand, activity, and ending on hand for an accounting period. Inventory accuracy typically approaches 99.9%.
How else can InOrder help detect theft?
Because InOrder’s Purchasing, Payables, and Inventory systems are all connected, you can compare what was ordered to what was received, to what you are paying your vendors.
The system tracks all purchase orders placed with your vendors, and any subsequent changes to those orders. Inventory receipt transactions are linked to purchase orders, recording what happened to each carton entering the facility. Vendor bills are entered into the system before or after inventory receipt. These bills get linked to the receipt and the purchase order. Any inventory that is received damaged is tracked as it gets routed back to the vendor for credit, and the credits are tracked. These processes enable control over what you receive and approve for payment with your vendors, stopping vendor billing fraud in its tracks.
Then these processes directly feed G/L, thwarting the rogue accountant who tries to skim by charging higher expenses on the G/L than the expenses actually incurred on your vendor bills, and then pocketing the difference.
Finally, InOrder’s tracking auditing enables you to isolate and trace other types of employee theft, such as generation of bogus customer refunds, gift cards, or credit memos issued to friends of employees. Seeing who performed a transaction and when is helpful, but forensic analysis of suspicious transaction patterns in the database can also help to isolate the employee(s) involved.
With a good ERP system, employees discover that they can trust the system, and you in the process. With their trust comes respect and confidence that their jobs will be secure and the business will continue to grow. A good ERP system helps you improve your customers’ shopping experience, achieve their trust that you keep your word about your products, and you take their business seriously.
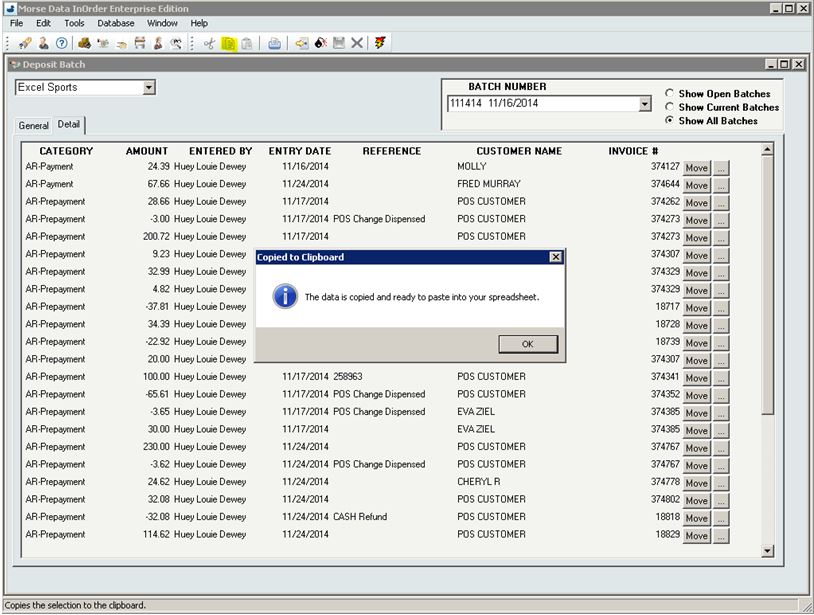
Quick Tip – Copying Deposit Batch Details to a Spreadsheet
Do you need to quickly get deposit batch details to a spreadsheet? To copy the details, use the copy shortcut (Ctrl+C) or click the copy button on the InOrder toolbar.
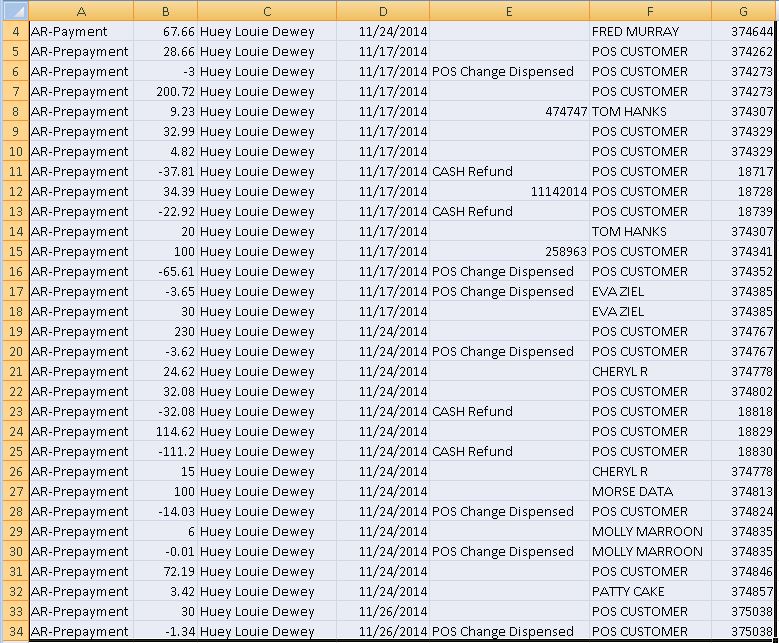
Then paste (CTRL+V) the details into your spreadsheet:
Every Item Counts With InOrder
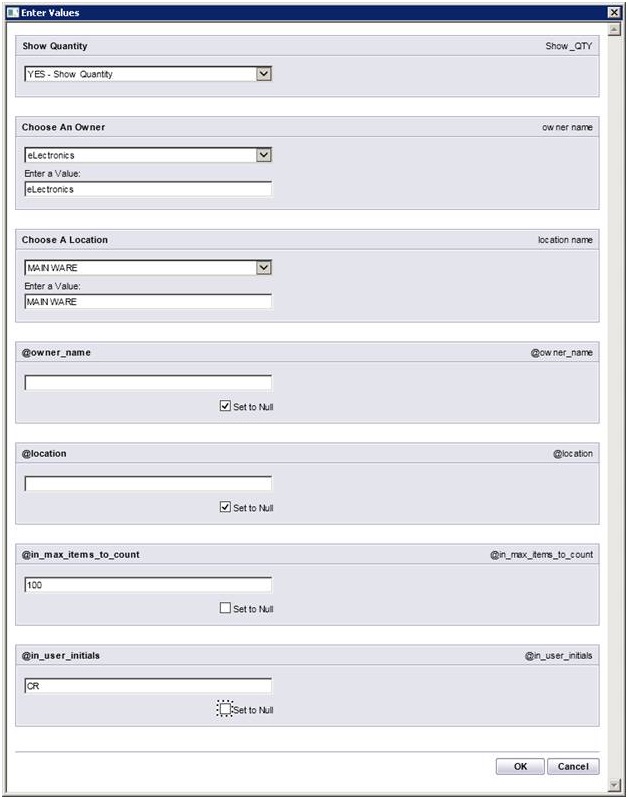
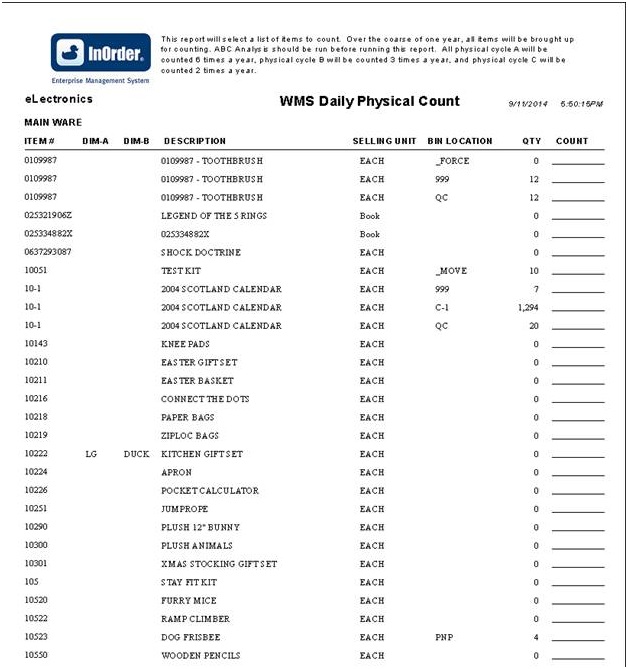
The Item Count function within InOrder may be used for period inventory counting, as well as continued inventory counting. For example, after daily warehouse activities (such as picking, packing, putaway, etc.) have been completed, the Warehouse Manager may generate a Daily Physical Count report to generate Inventory Tags for each RF user to complete that day.
InOrder RF allows RF personnel to complete item count tasks that have been assigned to them. The barcode of the bin is first scanned, then the barcode of the item is scanned and the quantity is entered.
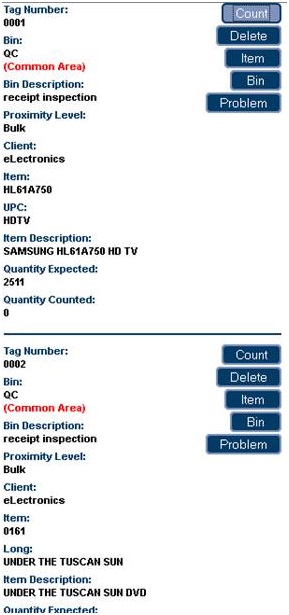 Item count tasks are generated via the Daily Physical Count report, which assigns inventory tags to RF users.
Item count tasks are generated via the Daily Physical Count report, which assigns inventory tags to RF users.
 Assigned tags are displayed on the InOrder [Inventory Tags] window. Unassigned items may also be counted manually.
Assigned tags are displayed on the InOrder [Inventory Tags] window. Unassigned items may also be counted manually.
The Daily Physical Count report template supports the Item Count function. New parameters include the maximum number of items to count and the initials of the user who will be counting.
For more information about any of these features, call 888-667-7332
or send email to support@morsedata.com.
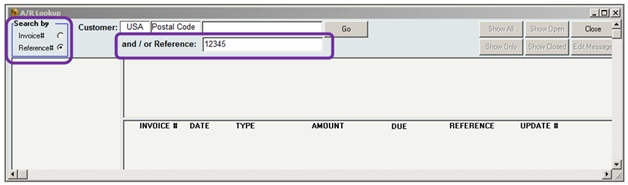
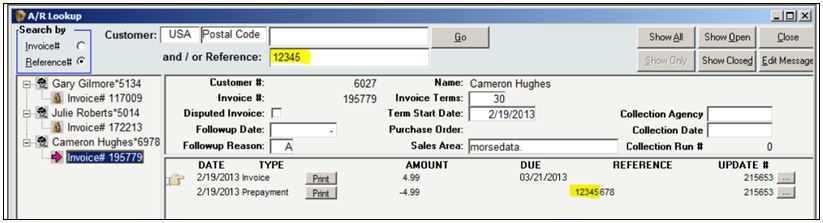
InOrder Quick Tip – Searching by Check Number
You may occasionally need to find an order by searching for a specific check number. If the check number was specified when the payment was entered, then finding that order is as easy as searching for the invoice. Here’s how:
- In A/R Lookup, select the Reference # option in the Search By box.
- Enter the check number in the Reference field.
All invoices containing that check number are listed in the search results.
10 Surprising Ways InOrder is Like Super Heroes

Super heroes always stand above the crowd and are favorites because they can do amazing things. Here are just a few of the many ways InOrder reminds us of these super heroes.
- Batman – Both are always available to save the day when a crisis arises.
- Captain America – Both have the determination and ability to improve. InOrder is always improving and adding surprising new tricks; just check out our blogs for some of our newest features. Our customers also get our monthly InOvation for a more thorough overview of new features.
- Green Hornet – Both have a sidekick who helps them along to solve the problems of the day. InOrder’s sidekick is Crystal Reports.
- The Hulk – Both have incredible strength and can handle unexpected workloads.
- Iron Man – Both are smart, and can conquer just about any order, warehouse, or customer challenge.
- Superman – Both are sighted in many places. InOrder can be seen operating in many places from Maine to Hawaii, from New York to Chicago to LA, all along the east coast and as far Northwest as Portland, Oregon. InOrder has even been seen operating in several European countries as well.
- Teenage Mutant Ninja Turtles – All are willing to go the extra mile to help you.
- Wolverine – Both have a complex history that resulted in success and made them what they are today, with experience and wisdom that others don’t have.
- Wonder Woman – Both have amazing versatility and can adapt quickly to do what is needed.
What other super heroes can you compare with InOrder?
Click here for more ways InOrder can help with your Enterprise Management.
InOrder Supports PCI DSS Compliance Efforts for Protecting Stored Cardholder Data
PCI DSS contains requirements for the protection of stored cardholder data using cryptographic keys. These keys must be changed at least once a year. This is a straightforward procedure for you and your key custodians using the InOrder Key Management Wizard.
The network administration / security personnel, along with the designated Key Custodians, run the InOrder Key Encryption Wizard to change the key. If a key is old or suspected to be compromised, it is replaced. This procedure is audited by the system so your PCI QSA can confirm it has been done.
The InOrder Key Management Wizard supports PCI DSS compliance efforts by assisting with the following tasks for handling cryptographic key material:
- Generation of strong cryptographic keys
- Secure cryptographic key storage by generating key encrypting keys
- Split knowledge and dual control of cryptographic keys
- Periodic cryptographic key changes
- Rendering cryptographic material irretrievable by retirement or replacement of old or suspected compromised cryptographic keys
- Re-encrypting historic data with new keys
- Requirement for cryptographic key custodians to acknowledge that they understand and accept their key custodian responsibilities
- Backup and restore of keys
- Audit of all key maintenance operations
- Required use of complex passwords
- Restricting key access to the fewest number of custodians necessary
- Storing keys securely in the fewest possible locations and forms
Please refer directly to PCI DSS for your responsibilities under these requirements. If you have specific questions relating to your responsibilities for PCI DSS compliance, please direct them to your Qualified Security Assessor (QSA).
Making Reports Run Faster When Comparing a DATE to a DATETIME in SQL
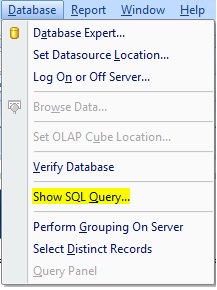
When Crystal Reports runs a report, it retrieves as much information as it can from the SQL Server and brings it back to the local machine to finish processing. Depending on the complexity of the report, this can mean a lot of processing taking place on your PC. As your database grows, you may notice that your reports aren’t running as fast as they once did. One way to speed up the running of a Crystal Report is to push as much as possible of the work down to the SQL Server.
There are a number of different ways to do this, not all of which we’ll discuss here. If you have a SQL professional in-house, you may choose to write the entire report selection as a SQL stored procedure or view and just using Crystal Reports as a viewing interface to display the results. If you’d rather keep the “building blocks” of the report in Crystal Reports, make sure your record selection is done wisely; don’t use formulas or data conversions on fields within the record selection. You can tell you’ve done this when you see most or all of your record selection in the WHERE clause of the “Show SQL Query” menu option.
 Here is an easy example using dates.
Here is an easy example using dates.
For most reports that have a date selection, you only want to choose a beginning and ending date, not date/time. But, most date fields in InOrder are date/time fields. Comparing date to date/time is a data conversion.
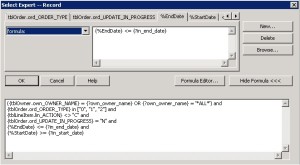
Here is a pretty common record selection, converting the date/time of an InOrder field to Date, and comparing it to the input parameters for start and end date: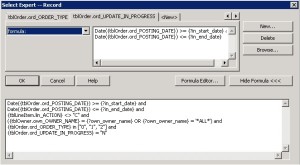
Here is its corresponding SQL Query. Note that it is not asking SQL Server to do any filtering of the results by date.
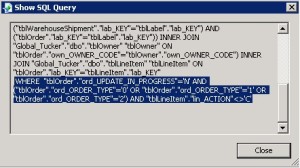 Now here is the same record selection using a SQL Expression.
Now here is the same record selection using a SQL Expression.
 Here is the corresponding SQL Query. It’s asking SQL to do the work to filter by date.
Here is the corresponding SQL Query. It’s asking SQL to do the work to filter by date.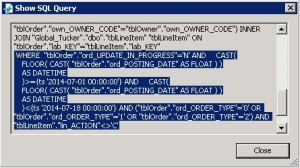
You can make your own SQL Expression to carry out calculations and conversions in the Field Explorer of Crystal Reports.
 Any time you need to use a formula or data conversion for record selection, sorting, grouping, or totaling – you may want to consider building a SQL Expression instead.
Any time you need to use a formula or data conversion for record selection, sorting, grouping, or totaling – you may want to consider building a SQL Expression instead.