Archive: September, 2016
Morse Data Corporation Named a Multichannel Merchant Top Commerce Platform for 2017
 We are proud to announce that we have been named a Multichannel Merchant Top Commerce Platform for 2017, part of a list of leading commerce platform providers selected by the editors of Multichannel Merchant. With this listing, users can see InOrder’s featured capabilities, ideal client types, equipment and systems, contact information, and more.
We are proud to announce that we have been named a Multichannel Merchant Top Commerce Platform for 2017, part of a list of leading commerce platform providers selected by the editors of Multichannel Merchant. With this listing, users can see InOrder’s featured capabilities, ideal client types, equipment and systems, contact information, and more.
To see what makes InOrder so special, call us at 888- 667-7332 for a free demo.
InOrder’s Advanced Shipping Notice Feature Improves Receiving Efficiency
In many cases, stock that will be arriving is (or could be, if you ask) preceded by advance notice from the vendor based on your POs to that vendor. This could be in the form of an email or a fax or a website. InOrder supports importing this data through EDI processes, where both you and your vendor(s) needed to have EDI programming set up ahead of time for automatic transmittal of POs to your vendors, and then PO acknowledgements, ASNs and/or Vendor Invoices back to you.
Industry surveys typically indicate that receiving efficiency can be significantly improved, by as much as 85%, when using an EDI vendor advanced ship notice process.
Yes, all of this could be automated, but what about your vendors who do not have the resources to set up this sophisticated EDI process?
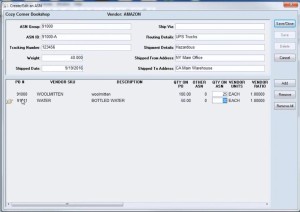
InOrder also supports manually adding and editing ASNs by selecting line items from that vendor’s open POs, and recording which open PO line item expected quantities are on each ASN, at the carton level.
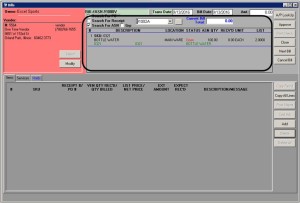
Optimally, for each ASN, the vendor assigns ID number(s) at the carton and/or the pallet, or shipment level. This way, your receiving team can know precisely what to expect in each carton they are receiving. They can generate the inventory receipt line items by simply scanning that carton or pallet ID, and then verify the contents.
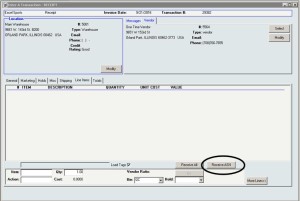
And for your accounting team, vendor bill line item entry also works with manually entered ASNs
For more information about using InOrder for ASNs, EDI, Receiving, and other features, please contact us for a free demo.
Morse Data Corporation Announces Additional Support for Credit Card Processing
InOrder now includes two new payment interfaces that support tokenization. With this update, clients using InOrder can process tokenized payments through Authorize.Net CIM and TransFirst TransExpress, in addition to its other payment processing interfaces.
The new Authorize.Net Tokenization gateway interface uses Authorize.Net’s Customer Information Manager (CIM) interface. CIM requires payments to be tokenized and does not support card present processing. There is no need for existing Authorize.Net Advanced Integration Method (AIM) users to switch to the new CIM interface unless they would like to tokenize. Further, Authorize.Net merchant accounts can use AIM or CIM (existing AIM users do not need to create a new merchant account with Authorize.Net to use CIM).
With the new TransFirst – TransExpress (TXP) interface, tokenization is optional and controlled by a checkbox when setting up the merchant information in the InOrder application.
In addition to these new payment interfaces, InOrder also supports three check processing gateways and several other credit card processors, including:
Credit Cards Processing Interfaces:
- Authorize.Net AIM
- Authorize.Net CIM (Tokenization)
- Bibit / RBS Worldpay
- Bluepay
- CyberSource
- First Data
- Litle PaymentTech
- TransFirst – ePay (Legacy)
- TransFirst – TransExpress
Check Processing Interfaces:
- Authorize.Net – ACH
- Authorize.Net – ACHT
- CyberSource – ACT
- My eCheck (Check 21)
- TransFirst – TransExpress – ACH
Other Interfaces:
- PayPal
Contact us for more information about processing payments with InOrder.
Technical Glitch – What’s Your Backup Plan for Processing Payments?
A WorldPay Technical Glitch lasted weeks, as reported in this article. What should businesses do? What would you do if that happened to your payment processor – at Christmas time?
You implemented appropriate security checks in your checkout process. So you have nothing to worry about when it comes to security, right? Maybe…
Do you have an Incident Response Plan? This is essential to detect and deter threats. It includes training, strong passwords, testing, planning, and securing your data. According to a report by Trustwave, this short list of things to include in your response plan can help contain a security breach from weeks to one day:
- Train your staff on the best security practices.
- Enforce passphrases or strong passwords (minimum of seven characters and combination of upper/lower case letters, symbols, and numbers). Also use two-factor authentication when accessing the network. Many compromises are caused by weak passwords.
- Secure your data. Test and scan to identify and fix flaws early.
- Use penetration testing on your system to identify vulnerabilities and understand how your data can be attacked.
- Plan your response to a breach and practice the Plan.
Customer trust is also a big deal. Customers don’t want to think about security – they want you to. And if you’re not easy to contact, they may go elsewhere. Make sure your customers can reach you immediately with any questions. Display your phone number where it can be easily and quickly seen. If a shopper has a question or problem navigating your site, make sure you can help.
It can be complicated for any business to keep up with all the cyber attacks and payment fraud going on around us, but you must be vigilant. Keep up with your PCI DSS requirements, have a security process and an incident response plan, and train your employees on them. A good ERP system can help with features such as fraud scoring, and it will support your PCI DSS efforts to keep your sensitive data safe.